Identity & Access Management
Identity and access management is about defining and managing the roles and access of individual users and the circumstances in which users are granted (or denied) those privileges. Users might be customers (CIAM) or employees. The core objective of IAM systems is one digital identity per individual. Once that digital identity has been established, it must be maintained, modified and monitored.
IAM (or CIAM in the context of customers) systems exist to provide administrators with the ability to change user’s roles, track activities, drive intelligence and enforce access policies on an ongoing basis. The systems also provide the ability to federate identity across multiple systems. This capability is increasingly in demand as organisations drive strong customer experiences.
Benefits of Identity & Access Management


Better customer experience
Reduce risk of exposure and improved security
Improved business intelligence through insights
Greater control over users and data
Reduce business administration costs
Reduce development complexity
How To Implement IAM
Most successful Identity and Access Management initiatives start with a clear vision and an understanding that IAM and CIAM are evolving capabilities rather than moment in time activities.
The driver for improved Identity and Access Management can vary, it could be
- Enablement of B2B
- Security and Risk
- Auditing and Compliance
- Digital Agility
- Increased Customer Experience
Whatever the driver, it’s important to define the vision from multiple perspectives before a path is walked. Business processes must be tied in from the start of the IAM program. Access privileges should be mapped to business roles in order to achieve role-based access control. Existing mappings should be explored to identify excessive privileges and redundant groups. The application estate should be fully understood prior to building the foundations for an IAM implementation.
Once the existing architecture is fully understood, it’s about building a strong foundation for adoption of an IAM capability. Evaluating the capabilities required and the probable future requirements are paramount. Items such as Single Sign-on, Multi-Factor Authentication, Identity Providers, Directory Services, Password Management, Key Management Solutions and Cryptography should be discussed using the help of subject matter experts in the IAM space.
Successful implementation of an IAM capability is usually a gradual process. Whilst it’s important to understand the full picture upfront, it’s also important not to do too much at once, jeopardising the success of the program.
As with any program of this size, it’s important to get the communication and stakeholder management right. One effective way of doing that is by delivering value quickly so that people take notice. A prime candidate for this would be self-service password reset abilities. It is likely this may already be in place to some degree, but might only have limited scope e.g. email password only. Enabling any degree of basic or enhanced self-service early gives an immediate impact to end users.
Following on from self-service, a typical pathway would involve
- Rationalising Directory Services, enabling an organisation-wide repository
- Enable role management
- Automate identify lifecycle process
- Establish an access management framework both internally and externally
- Implement Single-Sign On and other simplifications offering ease of access across domains


Common IAM Mistakes
Focusing on technology before understanding the business process and architecture is a very common mistake when it comes to IAM initiatives. IAM is much more than technology, and a technology-centric approach often results in user dissatisfaction and inefficiencies. This is largely due to adopting technical processes as opposed to running processes in a fashion more suitable to the organisation.
In terms of technology, failure to consider the supportability and maintenance of an IAM infrastructure can also lead to undesired outcomes. A solution that is onerous to maintain can result in the technology losing attention and ultimately being abandoned.
Another pitfall to avoid is the lack of a solid roadmap for the initiative. Without a clear phased plan and approach, the program can lose traction. Whilst there are clear benefits to IAM and CIAM, a lot of the important work is background work. It is therefore easy to become disillusioned and allow instant gratification projects to make all the noise. Something that can help with this is executive sponsorship. Strong leadership and investment can help overcome a lack of engagement and re-establish roadmaps.
Finally, not having the right skills or technical knowledge is a difficulty organisations face. The competency is not always easily obtained. Identity and Access Management is a niche discipline with overlapping security and integration requirements. It’s important to be aware of your competency in this space and ensure you have the roles lined up to meet your ambitions.


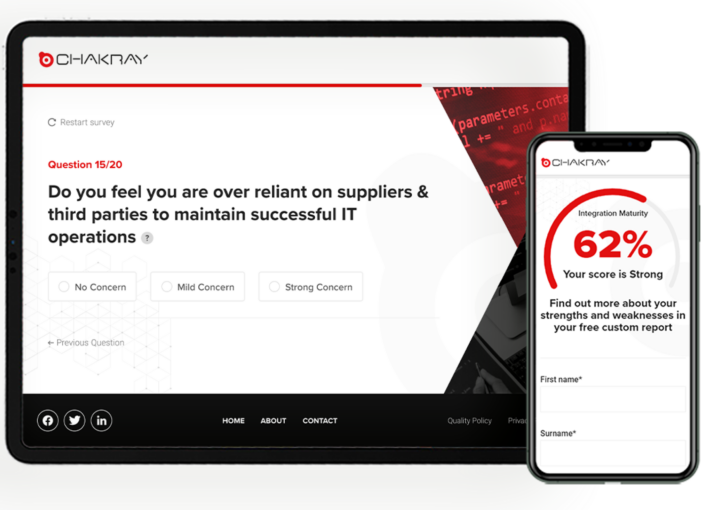
How Chakray Can Help
Chakray has worked with many organisations and completed numerous capability and technology implementations in this space. Our certified professionals have worked closely with organisations to understand their needs and help define a roadmap and implement solutions to achieve a strong capability in IAM & CIAM.
Our work in this space traverses many sectors delivering stronger systems and data security, business intelligence and perhaps most importantly a coherent and consistent customer experience. Whether you need help on the strategy or on the implementation side, Chakray can provide the roles and services you need to ensure a successful capability is achieved.
Get in touch
Talk to our experts
Contact our team to discuss your initiatives and find out how Chakray can help deliver your successful outcomes.
Get in touch